OAuth Permissions
Permission Management and Security in emma
emma uses the industry-standard OAuth 2.0 protocol to enable secure integration with external services. Through user consent-based authorization, you can access services with only the minimum required permissions.
How OAuth Works
emma connects securely with external services through a simple 3-step flow.
1
Authorization Request
User requests access to an external service
2
User Approval
Review and approve permissions on the provider's screen
3
Secure Connection
Connection completed securely with encrypted tokens
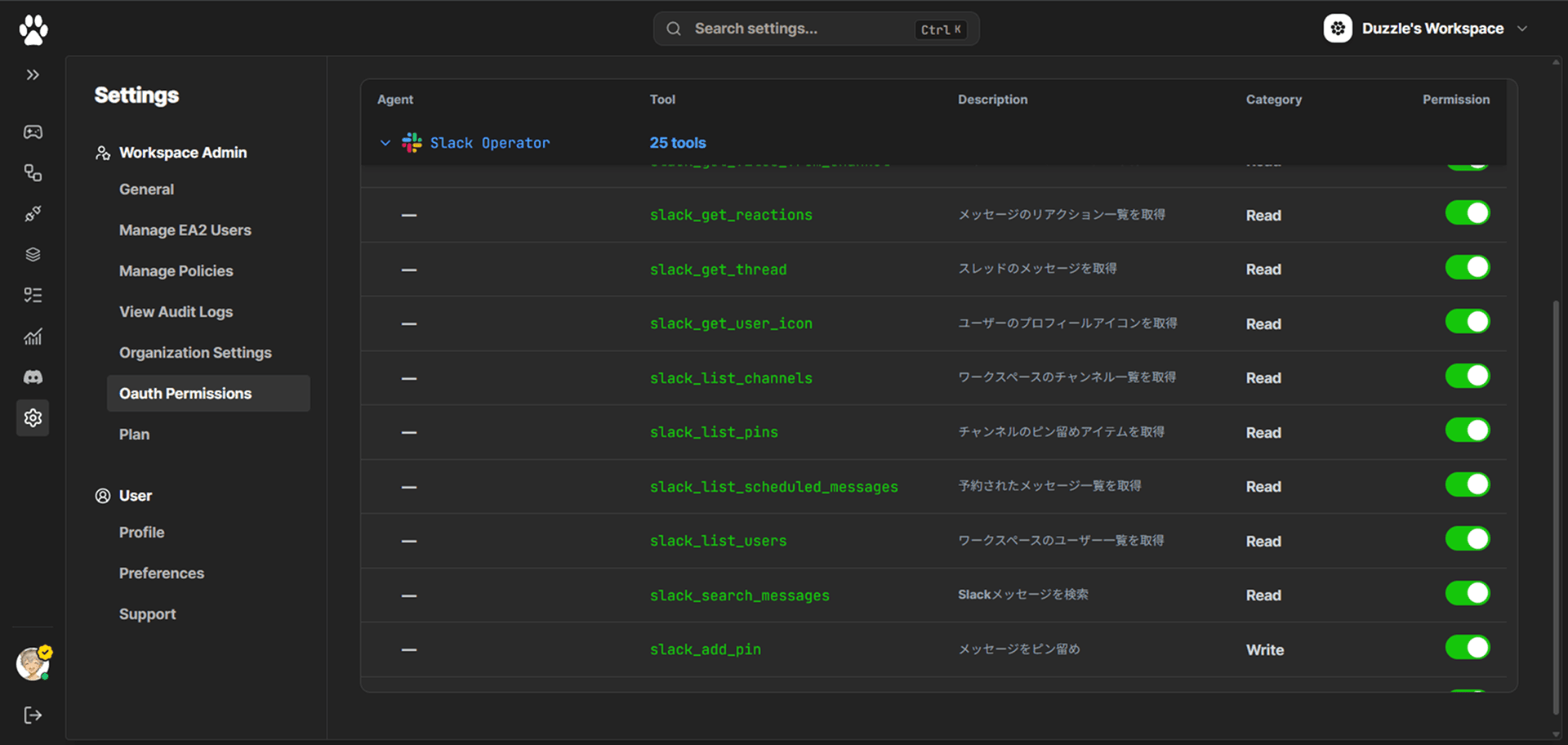
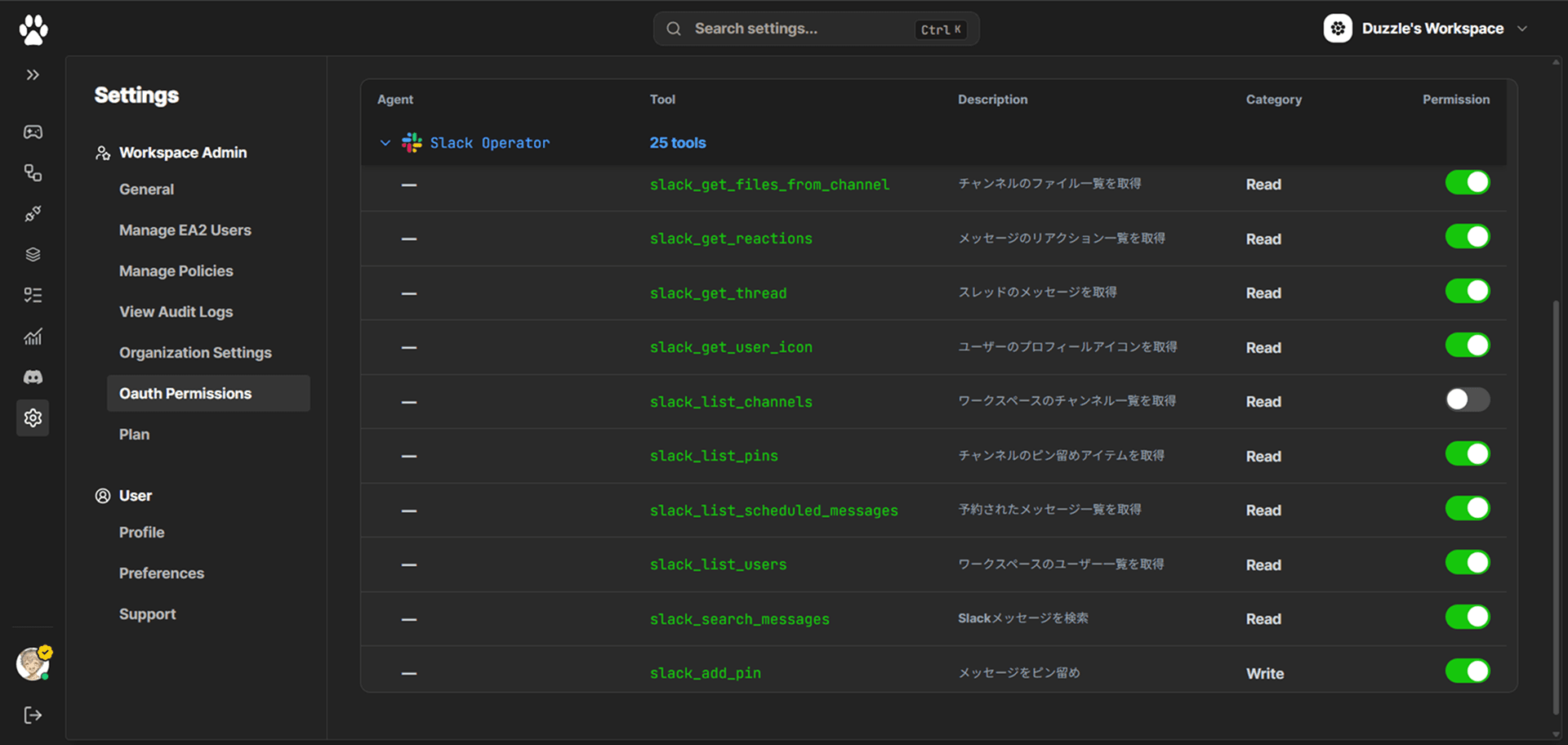
Permission Scopes
emma follows the principle of least privilege, requesting only the permissions needed. The following scopes are available.